Understanding Open Proxies: Risks to business and Infrastructure and how to block them
Introduction
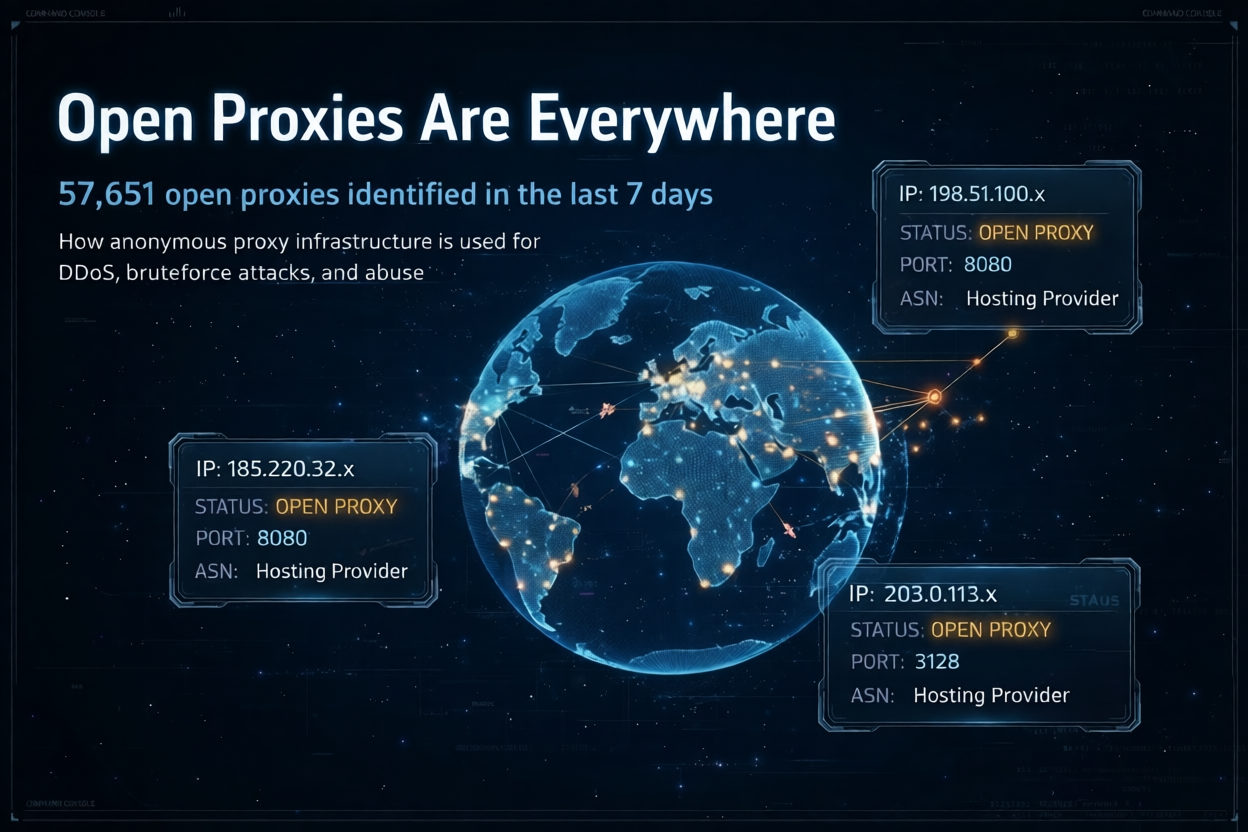
Modern organisations rely on proxies and reverse proxies to filter traffic, cache content and hide internal servers. But there’s a catch: open proxies, which are servers that are publicly accessible and let anyone relay traffic without authentication, have become a favourite tool for attackers. A widely used open proxy helps a criminal hide their IP address, bypass geographic restrictions or launch attacks anonymously. To give you an idea of scale, 57 651 open proxies were identified in the past week alone (data from Whatoblock’s Heartbeat feed). And look at what happened in January 2026, when Google took down the IPIDEA residential proxy network, Reuters reported that these residential proxies route traffic through hijacked consumer devices to mask malicious activity and bypass security defenses. In this article, we’ll explain how open proxies work, why they’re a problem for businesses and networks, and how you can block them automatically using tools like Whatoblock’s Heartbeat.
What Is an Open Proxy and Why Does It Exist?
An open proxy is simply a server that relays traffic for anyone on the internet. Unlike private or corporate proxies that restrict access to certain users or networks, an open proxy is publicly accessible and doesn’t ask for a password. When you send a web request through it, the proxy fetches the content on your behalf and hides your real IP address. Sometimes people misconfigure a private proxy and accidentally turn it into an open one. In other cases, compromised devices are turned into proxy servers by malware or malicious users deliberately create proxies to intercept or manipulate data.
Why Open Proxies Are Dangerous
Open proxies might seem like a handy way to browse anonymously, but they come with serious risks for both users and businesses. Here are some of the main risks you should be aware of:
Exposure of personal and corporate data
Many open proxies do not encrypt traffic, which means that any sensitive information you send, like passwords, banking details or session cookies, can be intercepted. Attackers controlling the proxy can record all activity and steal credentials or personal data. In a corporate setting, misconfigured proxies may log valuable data, such as authentication tokens, URLs with query strings or internal browsing activity. If these logs are not encrypted and properly access controlled, they can leak sensitive information.
Malware infection and malicious redirects
Attackers may configure open proxies to inject malicious scripts into the pages you visit, causing automatic malware downloads, fraudulent redirects or phishing campaigns. Malware such as TheMoon actively compromises end of life routers and installs proxies on them, the FBI warns that criminals use these compromised routers to conduct cyber crimes anonymously. The malware scans for open ports, infects vulnerable routers and then instructs them to act as proxies or scan other devices.
Used by attackers to target your network
Open proxies are not just a misconfiguration problem. Attackers actively exploit them to hide their identity and direct malicious traffic at your business. Because these servers treat all connections with equal fairness and do not inspect or filter content, cyber criminals frequently target open proxies to identify victims and share malware. They use chains of open proxies to send spam, phishing emails and botnet traffic, turning legitimate IP addresses into unwitting accomplices. Proofpoint explains that attackers route malicious traffic through unprotected proxies, masking their origin and framing the proxy’s IP, which contributes to blacklisting, service disruptions and reputational damage. To the target network, each request appears to come from a different benign IP, making traditional IP-based blocking ineffective.
When your website or API is under attack from thousands of open proxy IPs, the traffic volume can overwhelm application resources and complicate incident response. Attackers also use open proxies to orchestrate Layer 7 DDoS floods and credential stuffing campaigns, generating high concurrency with low per IP request rates. Without a proactive way to identify and block open proxies, security teams must sift through huge volumes of suspicious traffic to determine what’s legitimate and what’s not.
Loss of reputation and IP blocking
Because open proxies are frequently abused, many web services automatically block IP addresses associated with them. Attackers take advantage of this dynamic by routing malicious traffic through open proxies in order to avoid detection, thereby contaminating the reputation of those addresses. When your applications are bombarded by requests from IPs with poor reputations, automated defences may overreact and block legitimate traffic as well. Conversely, if a hosting provider or cloud network unknowingly hosts open proxy services, those IPs can be blacklisted by spam databases and threat intelligence feeds. This can result in abuse complaints, service disruptions and damage to your organisation’s IP reputation and brand.
Man in the Middle (MitM) attacks and shadow IT
Proxies intercept traffic by design. If a proxy is compromised, attackers can read, alter or inject content into the data stream, turning it into a man in the middle device. Employees may also connect to public proxies to bypass corporate controls or set up unauthorised proxy servers. These unmanaged entry points create shadow IT and become uncontrolled gateways into your internal network.
Real World Examples of Proxy Abuse
- Compromised routers via TheMoon malware: The FBI notes that end of life routers lacking security updates are being infected with TheMoon malware. This malware installs proxies on victim routers, allowing criminals to hide their identities and route traffic through compromised devices. Organisations that leave old routers unpatched risk becoming unwitting proxy nodes.
- Large residential proxy networks: In January 2026 Google disrupted IPIDEA, one of the world’s largest residential proxy networks. Reuters reported that residential proxy services route internet traffic through hijacked consumer IP addresses, masking malicious activity and bypassing security defenses. The operation reduced the available devices for the proxy operators by millions, illustrating both the scale of the problem and the importance of disrupting these networks.
Impact on Business Infrastructure
Open proxies threaten businesses in multiple ways:
- Floods of malicious traffic: Attackers spread their requests across thousands of open proxy IPs to bypass rate limits and hide their origin. This increases the volume of inbound malicious traffic, overwhelms your application resources and complicates incident response.
- Unmanaged entry points: Shadow IT proxies and unauthorised services become gateways for attackers to pivot into internal networks. Once inside, criminals can move laterally, exfiltrate data or deploy ransomware.
- Service disruption and performance issues: Proxy servers can become single points of failure. When misconfigured or overwhelmed, they cause outages and performance bottlenecks.
- Abuse requests and IP reputation: Hosting providers and ASN owners that unknowingly host open proxies may face abuse reports from other networks. Attackers’ use of these proxies contaminates IP reputation and may get entire subnets added to spam or threat blocklists, damaging the provider’s brand and disrupting legitimate customer traffic.
- Regulatory and legal risks: Exposure of personal data via unsecured proxies or failure to stop malicious traffic can result in regulatory penalties under data protection laws and increased liability.
Best Practices for Preventing Open Proxy Risks
- Avoid using free, unverified proxies. Many “free proxy” lists on the internet are unsafe and may be operated by attackers. Use reputable VPNs or corporate proxies that implement proper security controls.
- Patch and replace legacy hardware. The FBI recommends replacing end of life routers, applying security patches and disabling remote administration to prevent malware like TheMoon.
- Disable remote management and secure credentials. Use strong, unique passwords and disable password hints on network devices.
- Restrict proxy services to authorised users. Ensure that proxy servers require authentication and are not publicly exposed.
- Use encrypted protocols (HTTPS or SSL) and monitor logs. Encrypt traffic to mitigate man in the middle attacks and implement role based access controls on logs.
- Segment proxy infrastructure and implement redundancy. Isolate proxies, load balance them and monitor for anomalies.
- Educate staff and monitor for shadow IT. Train employees about proxy risks and enforce policies to prevent unauthorised proxy setups.
Automating Open Proxy Blocking with Whatoblock Heartbeat
Given the sheer number of open proxies in use, tens of thousands discovered in a single week, manual blocking is impractical. Whatoblock’s Heartbeat API provides a scalable solution. The Heartbeat API gives access to live IP threat intelligence and categorises IP addresses by threat type. The API supports multiple response formats, such as JSON, plain text, CSV and XML, making it easy to integrate with firewalls, SIEMs or reverse proxies.
The API’s category filter supports categories like OpenProxy, Tor_Exit_Node, Scanner and C2. Administrators can query the API for IP addresses flagged as open proxies within a specific time window, country or autonomous system. For example, a request like /apiv3/heartbeat?apiKey=KEY&time=24h&category=OpenProxy returns a list of recently observed open proxy IPs. The API even provides a plain text format where each IP appears on its own line, ideal for importing directly into firewall rules. Usage examples show how organisations can block high risk threats by downloading IP addresses and feeding them into their firewall or security tools.
The Heartbeat feed reports that 57.651 open proxies were identified in the last seven days, demonstrating the benefit of continuous monitoring. By automating the retrieval and blocking of open proxy IPs, businesses can dramatically reduce exposure. The API can be polled regularly to update block lists, and the info parameter can include metadata such as the number of tokens charged and category breakdowns.
This feed is valuable not only for companies defending their web applications but also for infrastructure providers. Hosting providers and autonomous system (AS) owners can query Heartbeat for open proxies within their IP ranges, identify misconfigured servers or compromised customer devices and take corrective action before abuse complaints arrive. Removing these proxies helps maintain a clean IP reputation, reduces the risk of being blacklisted and protects the provider’s brand. Similarly, defenders on the receiving end of attacks can download lists of open proxy IPs and feed them into firewalls, web application firewalls or reverse proxies to block malicious traffic at the edge.
Risks of Layer 7 DDoS Attacks for Businesses
Layer 7 DDoS attacks target the application layer rather than saturating network bandwidth. They often mimic legitimate user behaviour, which makes them harder to detect and allows attackers to disrupt specific components like login pages or search functions. According to Radware, application layer attacks account for nearly 60 percent of all DDoS attacks and can knock critical services offline. DataDome notes that 56 percent of DDoS attacks on Amazon Web Services in 2023 were sophisticated Layer 7 attacks, and the first half of 2024 saw a 200 percent increase in attack size. Cloudflare reported hyper volumetric HTTP attacks in 2025 exceeding 200 million requests per second and a 236 percent spike in total DDoS attacks between 2023 and 2025. These incidents can overwhelm application resources with relatively little traffic because each request triggers backend processes.
The business impact goes beyond temporary downtime. DataDome estimates that organisations face an average cost of about $6 000 per minute during a DDoS attack. Frequent application layer attacks degrade performance, cause lost sales for e commerce sites, trigger regulatory fines and damage customer trust. Because malicious requests blend in with normal traffic, security teams spend valuable time distinguishing legitimate users from attackers.
Brute Force and Credential Stuffing Attacks: Business Risks and Defences
Brute force attacks involve repeatedly guessing user credentials until one works. Modern attackers use automation, artificial intelligence and massive databases of stolen credentials to bypass weak authentication. BlackFog notes that these attacks are smarter, stealthier and more dangerous because criminals leverage AI and credential dumps to exploit weak login systems. The attack surface has expanded due to remote work, cloud services and IoT devices, creating many new entry points. In early 2025, a massive brute force campaign used nearly 2.8 million IP addresses to target VPNs, firewalls and edge devices from vendors such as Palo Alto Networks, Ivanti and SonicWall.
Variations such as credential stuffing, password spraying and reverse brute force allow attackers to reuse leaked passwords across many accounts or test common passwords at scale. Attackers now use machine learning models trained on leaked password dumps to generate highly targeted guesses. Stolen credentials are the leading cause of data breaches: analyses show that compromised credentials account for about 38 to 49 percent of security incidents. Each credential based breach costs organisations around $4.81 million. The dark web economy posts over 1 000 stolen credentials for sale every day, and most are sold for about $10. Such attacks can lead to ransomware infections and data exfiltration once criminals gain a foothold inside a network.
Conclusion
Open proxies have become a central part of the infrastructure that cyber criminals rely on. Because they’re misconfigured servers, compromised devices or dedicated proxy services, attackers can hide their identities, intercept traffic and launch attacks anonymously. For businesses on the receiving end, this means waves of malicious traffic from seemingly diverse IP addresses, higher resource consumption and the challenge of distinguishing legitimate users from attackers. Hosting providers and AS owners that unknowingly host open proxies also face abuse complaints and blacklisting, which can erode customer trust and damage brand reputation. Protecting your infrastructure calls for a mix of strategies: patch hardware, disable unused services, enforce access controls, encrypt traffic and monitor for shadow IT. Automated threat intelligence feeds like Whatoblock’s Heartbeat make it possible to continuously detect and block open proxies, whether you are defending your applications or cleaning up your IP ranges. By weaving these capabilities into your security stack, you can close the door on open proxies, protect your reputation and reduce your organisation’s attack surface.
